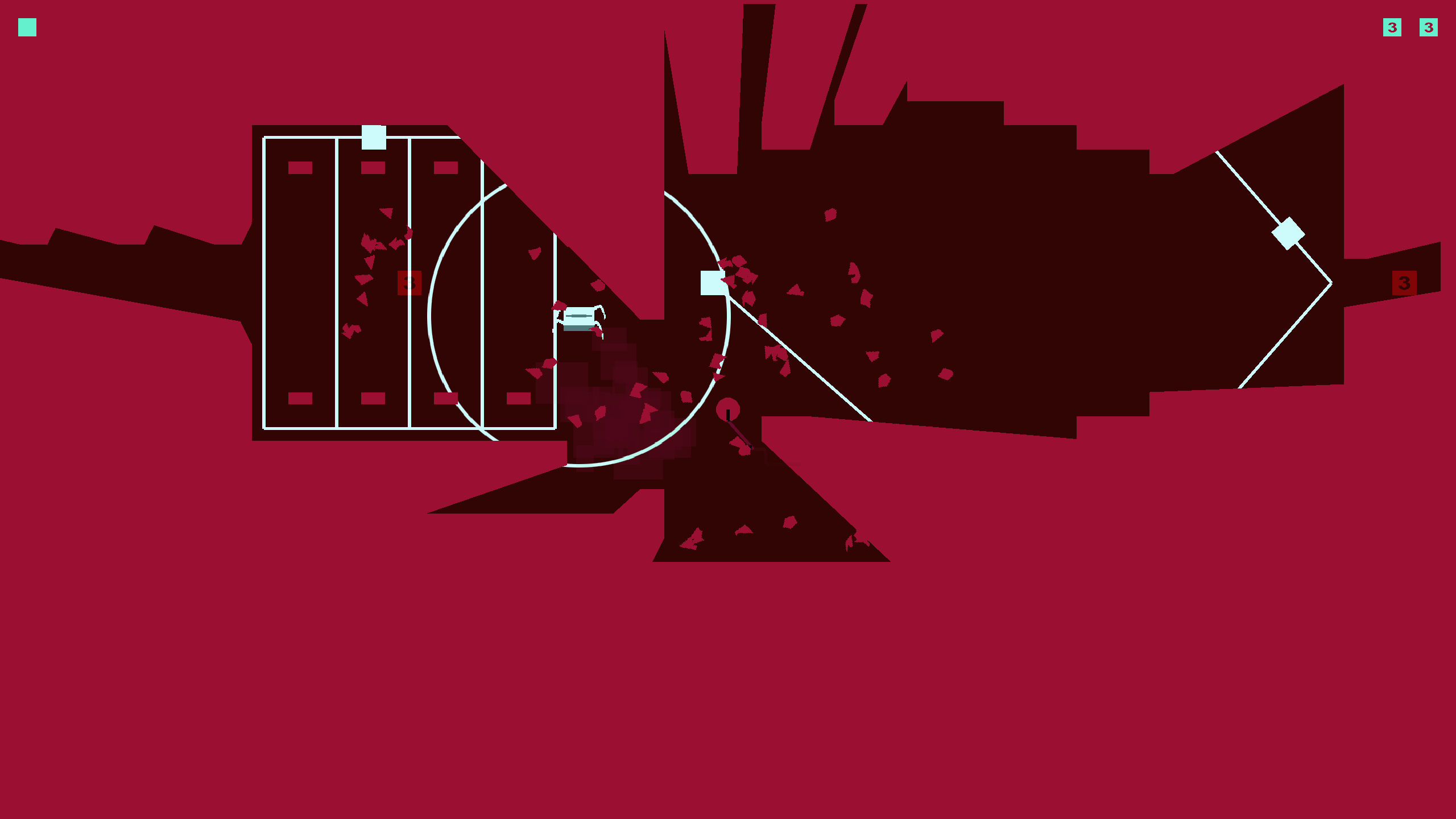
Stealth Prototype (2014) Mac OS
- Stealth Prototype (2014) Mac Os Catalina
- Stealth Prototype (2014) Mac Os Sierra
- Stealth Prototype (2014) Mac Os 7
OS X v10.5.1 and later include an application firewall you can use to control connections on a per-application basis (rather than a per-port basis). This makes it easier to gain the benefits of firewall protection, and helps prevent undesirable apps from taking control of network ports open for legitimate apps.
Configuring the application firewall in OS X v10.6 and later
Use these steps to enable the application firewall:
- Choose System Preferences from the Apple menu.
- Click Security or Security & Privacy.
- Click the Firewall tab.
- Unlock the pane by clicking the lock in the lower-left corner and enter the administrator username and password.
- Click 'Turn On Firewall' or 'Start' to enable the firewall.
- Click Advanced to customize the firewall configuration.
Configuring the Application Firewall in Mac OS X v10.5
Make sure you have updated to Mac OS X v10.5.1 or later. Then, use these steps to enable the application firewall:
- Choose System Preferences from the Apple menu.
- Click Security.
- Click the Firewall tab.
- Choose what mode you would like the firewall to use.
Advanced settings
Block all incoming connections
Q: Does enabling Stealth Mode on a Mac make it more secure? A: It does make it more secure but macOS is already so secure that it does not make much difference. macOS has a built in Application Firewall that cannot be turned off and is the defau.
Selecting the option to 'Block all incoming connections' prevents all sharing services, such as File Sharing and Screen Sharing from receiving incoming connections. The system services that are still allowed to receive incoming connections are:
- configd, which implements DHCP and other network configuration services
- mDNSResponder, which implements Bonjour
- racoon, which implements IPSec
To use sharing services, make sure 'Block all incoming connections' is deselected.
Allowing specific applications
/article-new/2020/12/macintosh-clear-prototype-4.jpeg?lossy)
Stealth Prototype (2014) Mac Os Catalina
To allow a specific app to receive incoming connections, add it using Firewall Options:
- Open System Preferences.
- Click the Security or Security & Privacy icon.
- Select the Firewall tab.
- Click the lock icon in the preference pane, then enter an administrator name and password.
- Click the Firewall Options button
- Click the Add Application (+) button.
- Select the app you want to allow incoming connection privileges for.
- Click Add.
- Click OK.
Stealth for Mac OS Free Stealth is one of the genres of computer games where the player is required to secretly complete tasks, try not to fall into the opponent’s field of vision, skillfully disguise himself and avoid noise. In many games of this genre, the player has a choice: pass secretly or conduct attacks openly. Razer Blade Stealth Intel Core i7. (15-inch Retina Mid 2014). Patched Radeon R280X AMD Radeon HD Tahiti XT Prototype Compute Engine OpenCL Mac OS X 64-bit. Apple’s leadership gave a deadline of October 31 (Halloween) for creating a working prototype of Star Trek. The group set to work porting the Mac OS to Intel processors. The task was a tedious one. Much of the Mac OS was written in 680×0 assembly code to make the computer faster and use less disk space. Stealth MIDI plug-in for Mac OS X is a plug-in for Apple's Core MIDI software to enable serial MIDI devices under Mac OS X. This driver allow to use most of the Serial MIDI interfaces with Mac OS.
You can also remove any apps listed here that you no longer want to allow by clicking the Remove App (-) button.
Automatically allow signed software to receive incoming connections
Applications that are signed by a valid certificate authority are automatically added to the list of allowed apps, rather than prompting the user to authorize them. Apps included in OS X are signed by Apple and are allowed to receive incoming connections when this setting is enabled. For example, since iTunes is already signed by Apple, it is automatically allowed to receive incoming connections through the firewall.
If you run an unsigned app that is not listed in the firewall list, a dialog appears with options to Allow or Deny connections for the app. If you choose Allow, OS X signs the application and automatically adds it to the firewall list. If you choose Deny, OS X adds it to the list but denies incoming connections intended for this app.
Stealth Prototype (2014) Mac Os Sierra
If you want to deny a digitally signed application, you should first add it to the list and then explicitly deny it.
Some apps check their own integrity when they are opened without using code signing. If the firewall recognizes such an app it doesn't sign it. Instead, it the 'Allow or Deny' dialog appears every time the app is opened. This can be avoided by upgrading to a version of the app that is signed by its developer.
Enable stealth mode
Enabling stealth mode prevents the computer from responding to probing requests. The computer still answers incoming requests for authorized apps. Unexpected requests, such as ICMP (ping) are ignored.
Firewall limitations
Stealth Prototype (2014) Mac Os 7
The application firewall is designed to work with Internet protocols most commonly used by applications – TCP and UDP. Firewall settings do not affect AppleTalk connections. The firewall may be set to block incoming ICMP 'pings' by enabling Stealth Mode in Advanced Settings. Earlier ipfw technology is still accessible from the command line (in Terminal) and the application firewall does not overrule any rules set using ipfw. If ipfw blocks an incoming packet, the application firewall does not process it.